QR codes, four ways they steal your card.
A sticker over the parking-meter QR on Avenue Montaigne. A fake table-tent in a Trastevere trattoria. A "parking fine" left on your rental-car windshield. A spoofed transit-kiosk at U-Bahnhof Alexanderplatz. Four QR-phishing variants across 12 countries, defeated by the same one-line check: read the URL preview before you tap.

Quishing (QR + phishing) runs four mechanics across 12 countries: parking-meter overlay, restaurant-menu spoof, fake-fine QR, and transit-ticket kiosk. The universal defense is one habit: read the URL preview banner before tapping. Genuine French parking is paybyphone.fr; Berlin transit is bvg.de; London transit is tfl.gov.uk. Any URL shortener (bit.ly, tinyurl, t.ly) or unrelated domain is the scam. Pay through official city or chain apps instead of QR codes whenever possible. Apps cannot be quished because the URL never changes. The clone-to-first-fraud window for quishing-captured cards is 6-24 hours; instant card-fraud alerts close the window in seconds.
"Paybyphone.fr" was the real domain. The sticker said paybyfone.fr.
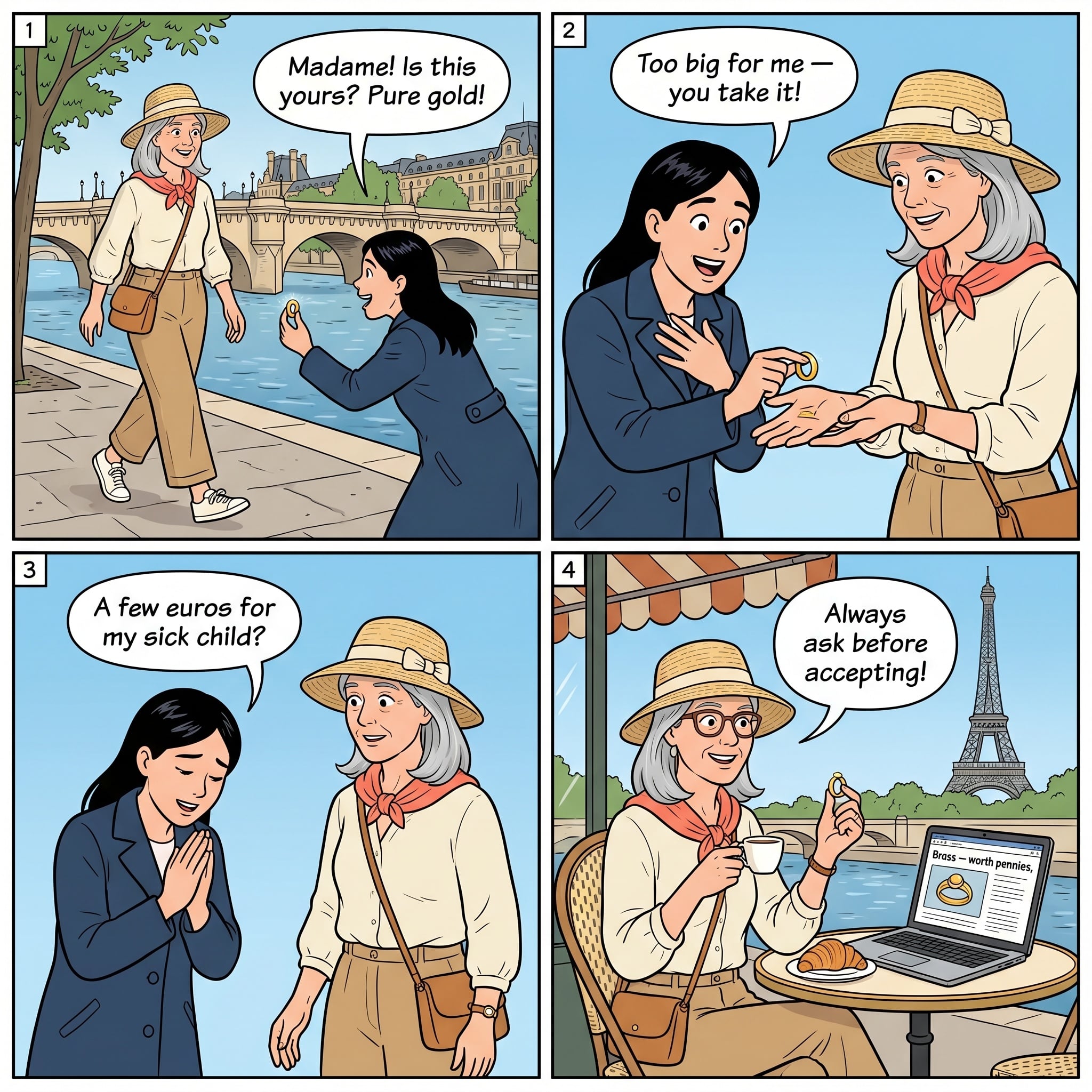
You park your rental car on Avenue Montaigne at 2pm on a Wednesday. The 8th-arrondissement parking signs are clear: pay-and-display via the meter or via the PayByPhone app. The meter has a QR sticker on the front face under "Scan to pay." You hold up your phone, scan, and the URL preview banner pops up at the top of the screen for half a second.
You miss it. You tap the banner. A page that looks identical to the genuine PayByPhone payment flow loads, asking for license-plate, parking duration, and card details. You enter the card number, CVV, expiry, and your billing zip. Confirmation page: "Parking session active until 16:00." You walk to the gallery on Rue de la Boetie.
That night at the hotel, your bank app pings: a 1,200-euro charge in Marseille; a second one in Lyon; the card is being run online for high-value digital goods. You freeze the card. The total fraud: about 4,000 euros across two hours before the freeze.
You go back the next morning to look at the meter. The QR sticker is glued over the legitimate one; the edges are slightly raised. Underneath is the genuine paybyphone.fr QR. The sticker on top loaded paybyfone.fr (one letter different) which captured the card details and dispensed the genuine PayByPhone payment from your stolen card so the meter actually showed paid time. The Mairie de Paris and the Prefecture de Police de Paris have logged the parking-meter quishing wave continuously since spring 2024; Le Parisien publishes monthly arrest counts. The 2025 EU Cyber Resilience Act explicitly addresses this attack vector.
That is the parking-meter quishing variant, executed at the global archetype: a high-foot-traffic Western European city with QR-payment infrastructure rolled out faster than the anti-tampering controls. The rest of this page is the four-mechanic playbook, the four other cities where it runs, and the URL-preview rule that defeats every variant.
Read the full Paris scam guide →Key Takeaways
The URL-preview rule
Quishing depends on you tapping the URL preview banner without reading it. The banner appears at the top of the screen for about half a second after you scan. The defense is one habit, repeated for every QR scan: pause, read the URL, then tap or cancel. The five-second routine eliminates every variant.
- Read the URL preview before tapping. Modern phones (iOS 11+, Android 8+) display the destination URL in a banner before opening. Read it. The legitimate domain matches the venue or city: paybyphone.fr for Paris parking, atac.roma.it for Rome buses, bvg.de for Berlin transit, tfl.gov.uk for London. Anything starting with a URL shortener (bit.ly, tinyurl, t.ly), an unrelated domain, or odd characters is the scam. Five-second pause defeats the entire phishing chain.
- Inspect the physical sticker for tampering. Quishing operators paste an overlay sticker on top of a legitimate QR code. Look at the edges; a glued-on overlay has a slight raised edge or air bubbles, while a printed-on QR is flush with the surface. The physical inspection takes 3 seconds and confirms what the URL preview suggests.
- Pay through the official app, not the QR. Every major-city parking, transit, and major-chain restaurant has a dedicated app: PayByPhone (France/UK), EasyPark (most of Europe), Parclick (Spain), MyCicero (Italy), BVG Fahrinfo (Berlin), TfL Go (London). Download the right app once at the start of your trip. Apps cannot be quished because the URL never changes.
- Never enter card details on a page reached via QR. Legitimate parking, transit, and restaurant payment flows in 2026 use Apple Pay, Google Pay, or saved card-on-file via the official app. They do not ask you to manually type your card number, CVV, and expiry on a web form. Manual card-form entry post-QR is the textbook phishing landing page.
- Set up real-time card-fraud alerts before you travel. Most major issuers (Chase, Amex, Capital One, Wise, Revolut) offer push notifications on every transaction. Enable them. The clone-to-first-fraud window for quishing-captured cards is typically 6-24 hours. Instant alerts let you freeze before the second charge lands.
The four mechanics
Different cities and different operator crews lean on different vectors within the same family. Here are the four sub-variants documented globally. Each has a recognition tell, a primary geography, and the routine step that defeats it.
1. Parking-Meter Quishing
An attacker prints a sticker matching the city's parking-payment graphic and pastes it over the legitimate QR code on a parking meter. Tourists scan, are routed to a phishing page that looks identical to the official payment site, and enter card details. The fraudulent transaction goes through (often the attacker even pays your real parking fee from the captured card to delay detection); the card is then cloned for further use.
Defense: use the official app (PayByPhone, EasyPark). Most reported in: Paris 8th and 16th arrondissements; London Westminster and Camden; Berlin Mitte and Charlottenburg; Madrid Salamanca.
2. Restaurant-Menu Quishing
A fake table-tent QR redirects to a menu page that ALSO captures card details when you "pay through the menu." The genuine restaurant-menu QR redirects to a menu-only page; if the menu page asks for credit card details to view full menu, place an order, or "unlock specials," it is the phishing variant. Rome and Barcelona variants run with high polish in tourist-zone restaurants.
Defense: ask for paper menu; pay at counter or via tableside terminal. Most reported in: Rome Trastevere and Trevi area; Barcelona Las Ramblas and Gothic Quarter; Lisbon Bairro Alto.
3. Fake-Fine QR
A fake parking-fine notice (or noise complaint or violation slip) is left on your windshield, hotel door, or rental-property mailbox. The notice is professionally printed, includes a city seal, and has a QR code for "easy payment." Scanning loads a phishing page asking for license-plate and card details. The real parking authority in most European cities sends fines by mail or registered notification, never via a windshield slip.
Defense: verify any fine on the city's official website manually. Most reported in: Paris arrondissements with high tourist-rental-car concentration; Berlin Mitte; Amsterdam Centrum; Cancun Hotel Zone.
4. Transit-Ticket Quishing
A quishing overlay surfaces in major transit hubs at QR-pay-at-kiosk options. Berlin BVG, Paris RATP, London TfL, and Madrid Metro all have official QR-pay options at certain kiosks. A quishing overlay redirects to a different domain, captures card details on a fake transit-payment page, and may even dispense a real ticket from the captured card to delay detection.
Defense: use the official transit app (BVG Fahrinfo, Bonjour RATP, TfL Go, Metro Madrid). Most reported in: Berlin Alexanderplatz and Hauptbahnhof; Paris Chatelet and Gare du Nord; London King's Cross and Victoria.
Where it runs
Quishing is an emerging 2024-2025 wave concentrating in cities that rolled out QR-payment infrastructure quickly between 2022-2024 without strong anti-tampering controls. Western Europe accounts for over 80% of documented variants; the wave is now spreading to North American and SE Asian tourist zones.
| Country | Documented variants | Iconic location pattern |
|---|---|---|
| 🇫🇷 France | 5 | Paris 8th and 16th arrondissement parking meters · RATP transit kiosks · tourist-zone restaurant tables |
| 🇮🇹 Italy | 4 | Rome Trastevere and Trevi area restaurants · ATAC bus-stop QRs · Milan Duomo parking |
| 🇩🇪 Germany | 3 | Berlin BVG transit kiosks at Alexanderplatz and Hauptbahnhof · Mitte parking-meters · Munich Marienplatz |
| 🇪🇸 Spain | 3 | Barcelona Metro and Las Ramblas restaurants · Madrid Salamanca parking-meter overlays · Sevilla tourist zone |
| 🇬🇧 United Kingdom | 3 | London Westminster and Camden parking-bay overlays · TfL platform QRs · Edinburgh Royal Mile |
| 🇳🇱 Netherlands | 2 | Amsterdam GVB transit-ticket kiosks · Centrum parking meters |
| 🇨🇿 Czech Republic | 2 | Prague parking and Old Town restaurant menus |
| 🇲🇽 Mexico | 1 | Cancun Hotel Zone parking-bay overlays |
Bar width is data-bound at 10 pixels per documented variant. The eight countries above account for 21 of 22 total variants, or 95% of the global atlas. The wave is fastest-growing in 2025-2026; expect new variants quarterly.
Four more cities, four more variants
The Avenue Montaigne scene above showed the parking-meter overlay variant. Here are four more cities where different sub-variants dominate. Each links to the full city scam guide.

You sit down at a small osteria in Trastevere at 7pm. The table has a small wooden tent with a printed QR labeled "Menu & Ordina" (Menu & Order). You scan. The page loads a stylish menu identical to the printed laminate at every other osteria in the area; below it is a "Pay your bill" button asking for full card number, CVV, expiry, and billing address. The page URL is a tilde-character variation of the real chain's domain. Rome and Trastevere have run the restaurant-menu quishing variant since 2024; the Polizia Postale (Italian cyber-fraud unit) has issued multiple advisories. The genuine restaurant-menu QR should redirect to a menu-only page; if asked for card details before placing an order, it is phishing. La Repubblica and Corriere della Sera publish monthly arrest counts of Rome quishing crews; the Polizia Postale 113 line accepts English-language reports. Defense: ask the waiter for a paper menu (every osteria has one); pay at the counter or via tableside terminal rather than through any QR-linked payment flow. The genuine Trastevere osterie are happy to print menus on request.
Read the full Rome scam guide →
You stand at a BVG ticket kiosk at U-Bahnhof Alexanderplatz at 9am. The ticket machine has a QR-pay sticker prominently displayed for "Einzelfahrkarte: Schnell zahlen mit QR" (Single ticket: Fast pay with QR). You scan. The URL preview shows bvg-ticket.com (note: not bvg.de, the real BVG domain). The page asks for card details rather than redirecting to Apple Pay or Google Pay. The Berliner Verkehrsbetriebe (BVG) has issued explicit warnings about quishing overlays at major U-Bahn stations; Tagesspiegel and Der Tagesspiegel Checkpoint have run multiple investigations of the variant since late 2024. The Bundesamt fur Sicherheit in der Informationstechnik (BSI) tracks quishing as one of the top four emerging fraud vectors for 2025. Defense: download BVG Fahrinfo at the start of your Berlin trip and use it for every ticket purchase. The app is the official channel; the URL never changes; quishing is impossible. Polizei Berlin LKA cyber-crime unit (030 4664-91-1100) accepts tourist-fraud reports.
Read the full Berlin scam guide →
You return to your rental car parked on Carrer de Ferran in the Gothic Quarter at 6pm. A printed slip is wedged under the wiper: "Aviso de multa de aparcamiento" (parking fine notice), with a Mossos d'Esquadra-style seal at the top, a QR code labeled "Pago rapido" (fast payment), and the warning text in three languages. You scan. The phishing page asks for license-plate, card details, and your home address. Real Barcelona parking fines are issued by the Servei Municipal d'Aparcament (SMASSA) and never delivered as a slip on your windshield with a QR code; they arrive by registered mail at the registered address. The fake-fine QR variant runs in the Gothic Quarter, El Born, and tourist-rental-car concentration zones. El Pais and La Vanguardia have published warnings; the SMASSA website has an explicit notice. Defense: do not pay any parking fine via a slip you find on your vehicle. Photograph it, look up SMASSA on the official Barcelona city website, and verify whether you actually have a fine on file. Real fines have a reference number you can verify online. The Mossos d'Esquadra Tourist Help line (+34 932 903 000, 24/7 English) accepts reports of the variant.
Read the full Barcelona scam guide →
You park your car on Margaret Street in Westminster at 11am. The pay-by-phone parking sign has a QR code below the area code; you scan and the URL preview shows pay-byphone.app (note the hyphen and the .app TLD; the real PayByPhone domain is paybyphone.com or paybyphone.co.uk). The phishing page mimics PayByPhone's interface and asks for card details. The Westminster City Council and Camden Council have both issued warnings about quishing overlays on parking signs; The Guardian ran a January 2025 investigation tracing the wave to coordinated crews operating across multiple London boroughs. Action Fraud (UK national fraud reporting at 0300 123 2040) accepts tourist-quishing reports; over 12,000 complaints in 2024 alone. Defense: download the real PayByPhone app once and use it for all London parking. The app cannot be quished. If you must use the QR for any reason, read the URL preview banner carefully and abort if anything looks unusual. The Westminster Parking Services line (020 7641 6500) confirms whether a code is genuine.
Read the full London scam guide →Red flags
If two or more of these signals fire when you are about to scan or have just scanned a QR code, cancel and use the official app instead. The compounding rule: a single signal might be a coincidence; two signals are a quishing setup.
- The QR is on a sticker rather than printed directly on the surface
- The sticker has visible raised edges or air bubbles
- The URL preview starts with a URL shortener (bit.ly, tinyurl, t.ly)
- The URL has subtle misspellings (paybyfone vs paybyphone)
- The URL has unusual TLDs (.app, .info, .xyz when you expected .fr or .com)
- The page asks for full card number + CVV + expiry on a web form
- The page does not offer Apple Pay or Google Pay as an alternative
- The QR is on a parking-fine slip you found on your windshield
- The QR is at an unusual location: stuck over an existing QR, in odd placement
- The transit kiosk QR you have not seen at this station before
The phrases that shut it down
Quishing defense is mostly technical (URL inspection) rather than verbal, but a clean phrase to ask staff for a paper alternative ends the in-restaurant menu variant immediately and signals to the venue that you have seen the QR play before.
If you got hit
You scanned a QR and entered card details, then realized the URL was wrong. The first hour matters most: the captured card will be cloned and used within 6-24 hours; instant freeze closes the window before subsequent fraudulent transactions.
Within five minutes: freeze the card immediately via your issuer app or 24/7 fraud line. The number is on the back of every card; save photos of all your card backs separately on your phone. Visa and Mastercard zero-liability policies cover unauthorized transactions made before the freeze.
Within thirty minutes: file a report with the local tourist-police line. The report number is required by some chargeback flows.
- Paris: Prefecture de Police 17 (24/7); SARIJ commissariats including 10 boulevard Strasbourg-Saint-Denis; English-language reports accepted.
- Rome: Polizia Postale 113 (Italian cyber-fraud unit); Carabinieri 112; Termini-area Polizia Ferroviaria 06-481-661.
- Berlin: Polizei Berlin LKA cyber-crime unit (030 4664-91-1100); Berlin Police 110.
- Barcelona: Mossos d'Esquadra Tourist Help, +34 932 903 000 (24/7, English).
- London: Action Fraud 0300 123 2040 (UK national fraud reporting line); Metropolitan Police 101 (non-emergency).
- Madrid: SATE (Sala de Atencion al Turista Extranjero), Calle Leganitos 19, +34 91 548 8537.
- Amsterdam: Politie Amsterdam, English-language reports accepted at the Centrum station off Spuistraat.
Within 24 hours: order a replacement card. Most major issuers (Amex, Chase, Capital One, Wise, Revolut) offer overnight emergency-replacement cards via DHL or FedEx to your hotel. The captured card is also a target for additional online fraud (phishing-derived data is sold in bulk on dark-web markets); enable real-time fraud alerts on the new card and monitor for unusual activity for 30 days. If you entered passport or other personal details, also alert your home country's identity-fraud reporting line: US IdentityTheft.gov; UK Action Fraud 0300 123 2040; Canada Anti-Fraud Centre 1-888-495-8501.
Related atlas entries
Sister entries in the Scam Atlas. Quishing overlaps with ATM skimming (both target card data) and with restaurant bill padding (both run in tourist-zone dining venues).
Sources
- Le Parisien, multi-month coverage of Paris parking-meter quishing (2024-2025) with arrest counts.
- Mairie de Paris and Prefecture de Police de Paris public guidance on parking-payment app preference.
- Polizia Postale (Italian cyber-fraud unit), advisories on restaurant-menu quishing in Rome and Florence (2024-2025).
- La Repubblica and Corriere della Sera, Rome quishing arrest reporting (2024-2025).
- Berliner Verkehrsbetriebe (BVG) public warnings on Hauptbahnhof and Alexanderplatz quishing overlays.
- Bundesamt fur Sicherheit in der Informationstechnik (BSI), 2025 emerging-fraud-vector reports.
- The Guardian, January 2025 investigation tracing London quishing crews across Westminster and Camden.
- UK Action Fraud annual report: 12,000+ quishing complaints in 2024.
- Mossos d'Esquadra and SMASSA Barcelona warnings on fake-fine QR slips on rental cars.
- r/travel, r/Paris, r/rome, r/berlin, r/barcelona, r/london continuing thread monitoring 2024-2026.
Get the full QR-safety playbook for your destination.
Each Travel Safety atlas covers every documented quishing variant in one country, plus the country's full scam catalog: pickpocket, taxi, ATM, restaurant, fake authority. Buy once, lifetime updates as scams evolve. $4.99 on Kindle.